المدونة
The Future of Trust: Why Zero-Trust Architecture is the Only Solution for B2B Platforms
In the evolving landscape of B2B platforms, traditional security models based on perimeter defense and implicit trust have become fundamentally inadequate. As platforms facilitate increasingly complex, high-value, and cross-border transactions between businesses, the attack surface has expanded dramatically. Supply chain attacks, credential theft, insider threats, and sophisticated nation-state actors have exposed the limitations of “trust but verify” approaches. Zero-Trust Architecture has emerged not as a trendy security buzzword, but as the only sustainable security model capable of protecting modern B2B platforms while enabling innovation, scalability, and regulatory compliance.

Future of Trust
This strategic and technical guide provides platform operators, Chief Information Security Officers (CISOs), compliance leaders, and technology executives with a thorough, audit-ready understanding of Zero-Trust principles and their practical application to B2B environments. The analysis focuses on why perimeter-based security fails in today’s interconnected ecosystem and how a properly implemented Zero-Trust model delivers superior protection, operational efficiency, and regulatory alignment.
Core Principle: In B2B platforms, trust is no longer a binary state granted at the network edge. It must be continuously evaluated, explicitly verified, and dynamically enforced at every transaction, user, device, and data interaction point. Zero-Trust is the only architecture that treats every access attempt as potentially hostile until proven otherwise.
Core Principles of Zero-Trust Architecture
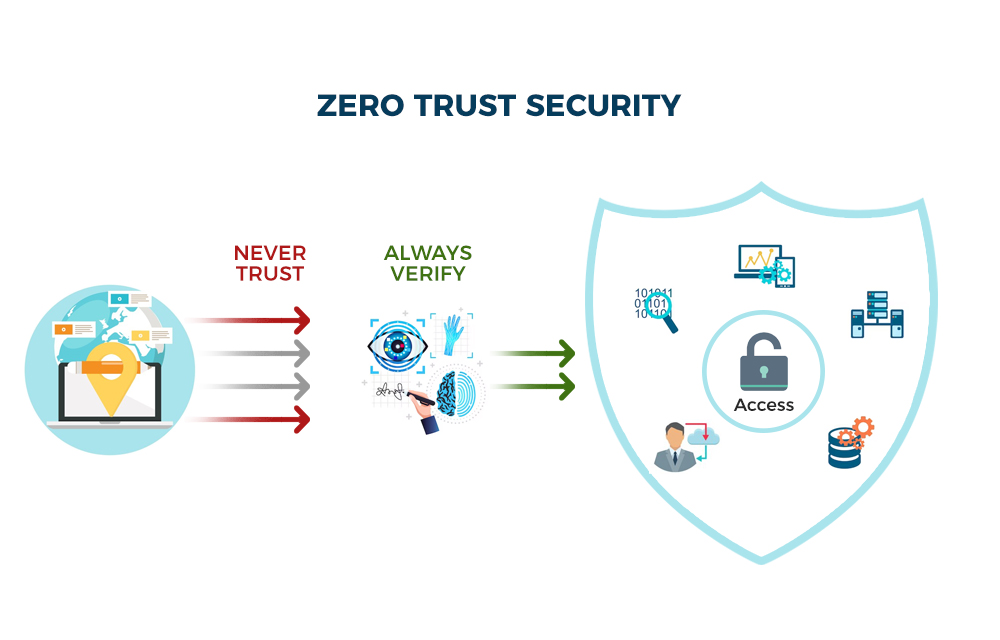
In today’s highly interconnected B2B platforms, traditional security models are no longer sufficient. Zero Trust Architecture (ZTA), formalized in NIST SP 800-207, is built on one core assumption: no user, device, application, or service should be trusted by default — regardless of its location or previous authentication history. The model shifts security from “trust but verify” to “never trust, always verify.”
Adopting Zero Trust for B2B platforms is essential to protect high-value transactions, complex supply chains, and multi-party ecosystems against credential theft, insider threats, and sophisticated supply chain attacks.
1. Never Trust, Always Verify
Every single access request must be explicitly authenticated and authorized in real time. This includes verifying user identity, device health/posture, location context, behavioral patterns, and risk signals before granting any access.
B2B Example: A supplier logging into your trade finance platform from a new IP or device must complete phishing-resistant MFA combined with device certificate validation — even if they accessed the system successfully the day before. This principle dramatically reduces the risk of lateral movement after an initial breach.
2. Least Privilege Access
Users and services receive only the minimum permissions necessary to complete their specific task. Access should be dynamic, context-aware, and time-limited (Just-in-Time / JIT access).
B2B Application: A supply chain partner can view and edit only the invoices and documents related to their transactions — never the entire database or other clients’ data.
3. Assume Breach
Design the entire architecture with the mindset that a breach has already occurred or is inevitable. Implement micro-segmentation to contain threats and limit the “blast radius” of any compromise.
Benefit for B2B Platforms: Even if attackers compromise a vendor account, they cannot easily move laterally to high-value financial workflows or sensitive customer information.
4. Continuous Monitoring and Validation
Trust is never static. Continuously monitor and re-validate all trust signals including user behavior, device compliance, threat intelligence, and transaction anomalies. Any deviation should automatically trigger policy enforcement or access revocation.
Advanced solutions integrate UEBA (User and Entity Behavior Analytics) و XDR (Extended Detection and Response) to achieve real-time visibility at scale.
5. Explicit Policy Enforcement
All access decisions are driven by clearly defined, centrally managed, and fully auditable security policies. A policy engine evaluates multiple contextual signals before allowing any action.
This creates a robust audit trail that is critical for regulatory compliance in trade finance and global supply chains (e.g., AML/CFT, sanctions screening).
Expanding the Principles with Real-World Context
While the five core principles form the foundation, successful Zero Trust implementations in B2B platforms go further by integrating these principles with modern technologies. For instance, combining Never Trust, Always Verify with continuous device posture assessment and real-time threat intelligence significantly strengthens protection against supply chain attacks that have increased dramatically in recent years.
Organizations that align their Zero Trust strategy with the CISA Zero Trust Maturity Model typically see faster progress across the five pillars: Identity, Devices, Networks, Applications & Workloads, and Data. This structured approach helps B2B platform operators move from initial pilot projects to enterprise-wide deployment more effectively.
نصيحة محترف: إن CISA Zero Trust Maturity Model organizes these principles across five pillars: Identity, Devices, Networks, Applications & Workloads, and Data. Aligning your implementation with this model accelerates maturity and compliance.
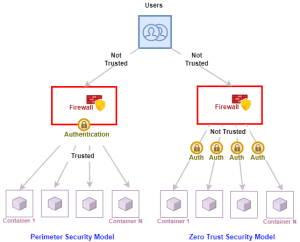
The Collapse of the Perimeter Security Model in B2B Platforms
Traditional security architecture assumed that threats originated primarily from outside a well-defined corporate perimeter. Firewalls, VPNs, and network segmentation were designed to keep “bad actors” out while implicitly trusting anyone or anything already inside the network. This model worked reasonably well when applications were monolithic, users were employees working from company offices, and data resided in centralized on-premises data centers.
Perimeter Security Model in B2B Platforms
Modern B2B platforms operate in an entirely different reality. Users include employees, partners, suppliers, customers, and third-party integrators accessing the platform from anywhere in the world. Data flows across multiple cloud providers, APIs connect disparate systems, and supply chains involve complex networks of contractors and subcontractors. The traditional perimeter has effectively dissolved.
In this environment, assuming trust based on network location or initial authentication creates dangerous blind spots. A compromised supplier account, a stolen API key, or an insider with excessive privileges can cause catastrophic damage. High-profile supply chain attacks have demonstrated that even well-defended organizations remain vulnerable when trust is granted too broadly. For platforms handling sensitive commercial data, financial transactions, or regulated information, these vulnerabilities represent existential risks. Related compliance challenges in high-volume trade environments are explored in False-Positive Avoidance in Sanctions Screening: AI-Driven Strategies for Compliant High-Volume Trade.

Zero-Trust Architecture
Implementing Zero-Trust in B2B Platforms: A Practical Framework
Transitioning to Zero-Trust requires a phased, risk-based approach rather than a big-bang replacement of existing systems.
Implementing Zero-Trust in B2B Platforms: A Practical Framework
Transitioning to Zero Trust should be phased and risk-based. The following 5-phase framework aligns with NIST and CISA recommendations and is tailored for complex B2B environments like trade finance and supply chain platforms.
A successful implementation typically includes the following stages:
Phase 1: Discovery and Visibility
Map all users, devices, applications, APIs, data flows, and dependencies. Identify high-value assets and establish a baseline of normal behavior. Tools like network discovery and asset management solutions are essential here.
Phase 2: Identity and Access Foundation
Implement strong, phishing-resistant authentication (passkeys, hardware keys, certificate-based auth). Deploy centralized Identity and Access Management (IAM) with just-in-time and just-enough access controls.
Phase 3: Micro-Segmentation and Policy Enforcement
Segment the platform at the application and workload level. Use policy decision points (PDP) and policy enforcement points (PEP) to evaluate access requests in real time based on multiple contextual signals.
Phase 4: Continuous Monitoring and Automation
Deploy advanced analytics for anomaly detection. Automate responses to low-risk events while keeping human oversight for critical incidents. Integrate with existing SIEM or XDR platforms.
Phase 5: Continuous Improvement and Compliance Integration
Regularly test controls through red team exercises, measure effectiveness with key metrics (e.g., mean time to detect/respond), and integrate Zero Trust decisions into your compliance and audit workflows.
Key Technologies That Enable Successful Implementation
Effective Zero Trust deployment in B2B environments often leverages technologies such as Software-Defined Perimeter (SDP), Secure Access Service Edge (SASE), Cloud Access Security Brokers (CASB), and advanced Policy Engines.
Integration with existing Identity providers, SIEM/XDR platforms, and API gateways allows organizations to enforce policies consistently across cloud, on-premises, and hybrid environments.
Expected Outcomes: Organizations that complete a structured Zero Trust rollout typically report reduced attack surface, faster incident response times, improved compliance posture, and greater confidence in enabling secure partner collaboration.
Why B2B Platforms Are Particularly Vulnerable Without Zero-Trust
B2B platforms operate in complex, multi-party environments involving suppliers, partners, financial institutions, and customers — often with varying levels of security maturity. Traditional perimeter-based security, designed for closed on-premises systems, fails to protect these dynamic ecosystems.
Industry reports indicate that over 60% of large enterprises are actively planning measurable Zero Trust programs by 2026, largely due to the sharp rise in supply chain attacks and credential-based breaches.
- Multi-organization collaboration: Different parties with inconsistent security controls share the same platform, creating unpredictable trust boundaries.
- High-value transactions: Trade finance, cross-border payments, and supply chain operations routinely involve millions of dollars per transaction, making them attractive targets for cybercriminals and nation-state actors.
- Complex API ecosystems: Hundreds or thousands of APIs become potential entry points for API abuse and injection attacks if not secured with Zero Trust policies.
- Third-party and supply chain risk: Expanding partner networks exponentially increase the attack surface.
- Regulatory and compliance pressure: Requirements such as GDPR, AML, and sanctions screening demand granular visibility, auditability, and strict access controls.
Without Zero Trust, a single compromised vendor credential can cascade across the entire platform. Micro-segmentation combined with continuous verification significantly reduces this risk by isolating threats and preventing lateral movement.
Real-World Impact of Perimeter Failure in B2B
The dissolution of the traditional perimeter has turned many B2B platforms into high-value targets. A single compromised third-party credential can lead to lateral movement across interconnected systems, exposing sensitive trade data, financial records, and customer information.
Statistics show that supply chain attacks rose sharply, making Zero Trust not just a best practice but a business necessity for platforms handling cross-border transactions and complex partner ecosystems.
By shifting to a Zero Trust model, B2B platforms can achieve granular visibility and control that perimeter-based defenses simply cannot provide, reducing both the likelihood and the potential impact of breaches.
Statistics for context: Gartner predicts that by 2026, 81% of organizations will have active Zero Trust initiatives, citing reduced breach impact and improved agility as key drivers.
90-Day Zero-Trust Readiness Checklist for B2B Platforms
Days 1–15: Discovery
- Map all users, devices, APIs, and data flows
- Identify high-value assets and critical business processes
- Assemble cross-functional Zero-Trust team
Days 16–45: Foundation Building
- Implement modern identity and access management
- Deploy initial micro-segmentation controls
- Establish centralized policy engine
Days 46–75: Testing and Refinement
- Run controlled pilots on selected high-risk workflows
- Measure impact on user experience and security posture
- Refine policies based on real-world data
Days 76–90: Scaling and Governance
- Expand Zero-Trust controls across the platform
- Integrate with existing compliance and audit systems
- Establish ongoing monitoring and improvement processes
Measuring Success in the First 90 Days
Track key metrics during your initial Zero Trust journey, including the percentage of assets inventoried, number of high-risk workflows protected with micro-segmentation, reduction in excessive permissions, and improvement in mean time to detect anomalous access attempts.
Regular reviews and adjustments based on real usage data will ensure the program delivers both security improvements and minimal disruption to business operations on your B2B platform.
Frequently Asked Questions (FAQ) About Zero Trust Architecture for B2B Platforms
Here are answers to the most common questions B2B platform operators, trade finance teams, and supply chain professionals ask when considering a move to Zero Trust.
What is Zero Trust Architecture and why is it critical for B2B platforms?
Zero Trust Architecture (ZTA), as defined in NIST SP 800-207, assumes no user, device, application, or service is trusted by default — regardless of location. Every access request must be explicitly verified. For B2B platforms handling high-value transactions and multi-party supply chains, this model eliminates implicit trust and dramatically reduces the risk of lateral movement after a breach, which is a major vulnerability in traditional perimeter-based systems.
How does Zero Trust differ from traditional perimeter security in B2B environments?
Traditional perimeter security relies on a “castle-and-moat” model that trusts anything inside the network. In contrast, Zero Trust verifies every request continuously using identity, device posture, context, and risk signals. In B2B platforms, this prevents a single compromised supplier credential from exposing the entire ecosystem, providing micro-segmentation and least-privilege access that perimeter models cannot deliver.
What are the core principles of Zero Trust Architecture?
The five core principles are:
1. Never Trust, Always Verify — explicit authentication for every access.
2. Least Privilege Access — grant only the minimum permissions needed.
3. Assume Breach — design as if a compromise has already occurred.
4. Continuous Monitoring and Validation — re-verify trust signals in real time.
5. Explicit Policy Enforcement — base all decisions on auditable, centralized policies.
These principles, supported by the CISA Zero Trust Maturity Model, are especially effective for protecting complex B2B workflows in trade finance and global supply chains.
Is Zero Trust suitable for B2B platforms with many third-party partners and suppliers?
Yes — in fact, it is one of the best use cases. B2B platforms involve numerous external partners with varying security maturity. Zero Trust enables secure collaboration by applying just-in-time access, micro-segmentation, and continuous verification, reducing supply chain attack risks while maintaining audit trails for AML/CFT and sanctions compliance.
How long does it take to implement Zero Trust in a B2B platform?
Implementation is a phased journey, not a one-time project. Many organizations see meaningful results within the first 90 days using a structured checklist focused on discovery, identity foundation, micro-segmentation, monitoring, and governance. Full enterprise-wide maturity typically takes 12–24 months, depending on platform complexity and legacy systems.
What are the main challenges when implementing Zero Trust for B2B?
Common challenges include cultural resistance to moving away from “trusted” internal networks, integration with legacy systems, potential initial latency concerns, and the need for cross-functional buy-in. These can be mitigated by starting with high-value workflows (e.g., trade finance modules), running controlled pilots, and measuring both security gains and user experience impact.
Does implementing Zero Trust improve compliance and audit readiness for B2B platforms?
Absolutely. Zero Trust creates detailed, real-time audit trails of every access decision based on explicit policies. This significantly strengthens compliance with regulations such as GDPR, AML/CFT requirements, and sanctions screening — areas that are critical for B2B platforms involved in cross-border transactions and supply chain finance.
Can Zero Trust negatively impact user experience or platform performance?
When implemented correctly with modern tools (such as SASE, SDP, and intelligent policy engines), Zero Trust has minimal impact on performance and can even improve UX through seamless, context-aware access. The key is using risk-based and just-in-time controls rather than adding friction to every login.
How can I get started with Zero Trust on my B2B platform?
Start with the 90-Day Zero Trust Readiness Checklist: focus first on asset discovery and visibility, then build a strong identity foundation with phishing-resistant MFA, and gradually apply micro-segmentation to critical APIs and workflows. Align your efforts with NIST SP 800-207 and the CISA Zero Trust Maturity Model for best results.
Have more questions? Feel free to contact our team for a personalized Zero Trust readiness assessment tailored to your B2B platform.
Conclusion: Zero-Trust as the Foundation of Future B2B Trust
The era of implicit trust in B2B platforms has ended. As platforms become more interconnected, handle higher-value transactions, and operate across more jurisdictions, the limitations of traditional perimeter security have become impossible to ignore. Zero-Trust Architecture offers the only sustainable model capable of protecting modern B2B platforms while enabling the innovation and collaboration that drive their value.
Implementing Zero-Trust is not a simple technology upgrade — it is a fundamental shift in how organizations think about security, identity, and access. Companies that embrace this shift with discipline, transparency, and a focus on measurable outcomes will build platforms that are not only more secure but also more agile, compliant, and trusted by their users.
The future of B2B platforms will be defined by those who replace outdated assumptions of trust with continuous, explicit verification. Zero-Trust is not the end of trust — it is the beginning of a more mature, resilient, and verifiable form of digital trust that can scale safely in an increasingly complex world.
Platforms purpose-built for secure, compliant B2B operations provide the foundational infrastructure necessary to implement Zero-Trust principles effectively. Organizations seeking to strengthen the security and trustworthiness of their B2B platforms are encouraged to adopt integrated solutions that combine advanced security capabilities with operational excellence and regulatory alignment.
Request a Confidential Zero-Trust Readiness Assessment for Your B2B Platform
