المدونة
The $500,000 Fake CEO: How Real-Time Deepfake Video Calls Are Challenging Corporate KYC

In an era of rapid technological advancement, corporate know-your-customer (KYC) processes have become a critical line of defense against financial crime. Yet the emergence of real-time deepfake technology has introduced a sophisticated new vector: the impersonation of high-level executives during video verification calls. A single successful deepfake attack can enable fraudsters to authorize multi-hundred-thousand-dollar transfers, open corporate accounts, or approve high-value transactions — all while appearing as the legitimate CEO or CFO on a live video feed. This guide examines the reported mechanics of such attacks, their compliance implications, and — most importantly — the audit-ready detection and mitigation frameworks that regulated entities can deploy to protect themselves while supporting legitimate business activity.
Deepfake Video Calls
This operational analysis is written from a strictly compliance-first perspective. It provides financial institutions, virtual asset service providers, trade-finance platforms, and corporate treasury teams with practical, regulator-neutral strategies for strengthening executive identity verification. Every recommendation is designed to comply with FATF standards, Travel Rule obligations, OFAC and EU sanctions guidance, and applicable local AML/CFT requirements. The focus is on risk mitigation, not speculation or sensationalism.
Compliance-First Principle: Real-time deepfake threats do not invalidate video KYC; they require layered, explainable detection controls that distinguish genuine human presence from synthetic media without creating unnecessary friction for legitimate executives.
Understanding Real-Time Deepfake Executive Impersonation
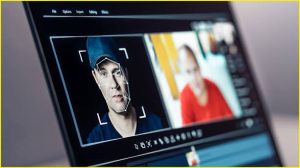
Real-time deepfake attacks involve the live generation of synthetic video and audio that overlays a perpetrator’s face and voice onto the likeness of a legitimate executive. Using generative AI models trained on publicly available photos, videos, and voice samples of the target CEO or CFO, attackers can create a convincing live feed that responds interactively to instructions such as “turn your head,” “repeat this phrase,” or “show your ID document.”

Real-Time Deepfake
The reported attack flow typically follows these steps:
- Acquisition of high-quality source material of the target executive through open-source intelligence or data breaches.
- Deployment of real-time deepfake software capable of processing video at 30+ frames per second with minimal latency.
- Spoofing of device metadata, camera feeds, and background elements to bypass basic anti-spoofing checks.
- Participation in a corporate video KYC or approval call while the synthetic feed is presented to the verifier.
- Authorization of high-value transactions or account openings once identity appears verified.
The financial impact can be immediate and severe. A single successful impersonation has been reported to enable transfers exceeding $500,000 before detection. For compliance teams, the challenge lies in the speed and realism of these attacks, which can defeat traditional liveness checks that rely solely on eye-blink detection or basic motion analysis.
For a deeper technical breakdown of related biometric threats, see our earlier analysis in Deepfake KYC: Real-Time Deepfake Identity Fraud and Audit-Ready Detection Strategies for AML/CFT Compliance.
Why Corporate KYC Remains Vulnerable in 2026
Many corporate onboarding and approval processes still rely on video calls that were designed to counter static fraud rather than real-time synthetic media. Legacy systems often lack multi-modal liveness detection, behavioral biometrics, or environmental signal validation. Even advanced platforms can be bypassed when attackers combine high-quality generative models with device spoofing and metadata manipulation.
The problem is compounded by the high-stakes nature of executive-level verification. A call involving a CEO or CFO authorizing a large transfer receives less scrutiny than a routine retail onboarding. Attackers exploit this asymmetry, targeting organizations with significant financial exposure and relatively streamlined executive approval processes.
Regulatory expectations have evolved, but implementation lags. Institutions are expected to apply enhanced due diligence for high-value or high-risk transactions, yet many still lack the technical controls necessary to detect sophisticated real-time deepfakes. This gap creates both compliance risk and financial exposure. For related challenges in sanctions screening during high-volume trade, refer to False-Positive Avoidance in Sanctions Screening: AI-Driven Strategies for Compliant High-Volume Trade.
Regulatory Expectations and Red-Flag Indicators
Regulators require institutions to maintain robust identity verification controls, particularly for executive-level or high-value transactions. Key obligations include multi-factor liveness assurance, behavioral analysis, and the ability to generate explainable audit logs for every verification decision. When real-time deepfakes are suspected, enhanced secondary verification — such as knowledge-based authentication or device-binding checks — becomes mandatory.
Common red-flag indicators include:
- Subtle desynchronization between lip movement and audio.
- Unnatural micro-expressions or lighting inconsistencies on facial features.
- Requests originating from devices with histories of anomalous verification attempts.
- High-value transactions authorized shortly after a new or unusual video verification.
- Metadata anomalies in the video stream (codec signatures, hardware identifiers).
Institutions that treat these indicators as escalation triggers — rather than routine approvals — significantly reduce exposure. Contractual and policy safeguards for managing executive impersonation risk are explored in Snapback Risk in the Iran-US-Israel Ceasefire: A Strategic Contract Management Guide for CEOs and Investors.
Comparative Risk Matrix: Traditional Video KYC vs. Deepfake-Resilient Verification
| أسبكت | Traditional Video KYC | Deepfake-Resilient Framework | Compliance Benefit |
|---|---|---|---|
| Liveness Detection | Basic motion and blink analysis | Multi-modal AI (facial, behavioral, environmental) | Substantially lower false negatives |
| False-Positive Rate | معتدل | Low through contextual scoring | Improved executive user experience |
| Audit Trail | Basic video recording | Explainable AI decision logs with metadata | Full regulatory defensibility |
| قابلية التوسع | Limited by manual review | Automated with human-in-the-loop escalation | Operational efficiency at volume |
For additional context on privacy-enhancing assets that may intersect with executive verification flows, see Privacy Coins on Decentralized Exchanges: Understanding the Technique and Implementing Audit-Ready Detection Strategies for AML/CFT Compliance.
Step-by-Step Playbook: Implementing Audit-Ready Deepfake Detection for Corporate KYC
Phase 1: Risk Assessment and Process Mapping
Inventory all executive-level video verification touchpoints. Classify risk by transaction value, counterparty jurisdiction, and product type.
Phase 2: Multi-Modal Liveness Technology Deployment
Integrate systems combining facial landmark analysis, behavioral biometrics, and environmental signal validation.
Phase 3: Real-Time AI Anomaly Detection
Deploy models trained to identify temporal inconsistencies, lighting physics anomalies, and synthetic media artifacts.
Phase 4: Metadata and Device Fingerprint Validation
Implement hardware-level checks to detect spoofed camera feeds or injected synthetic streams.
Phase 5: Contextual Risk Scoring
Combine biometric results with sanctions screening, historical behavioral patterns, and transaction context.
Phase 6: Explainable AI and Human Escalation
Ensure every automated decision includes human-readable reasoning chains for audit purposes.
Phase 7: Continuous Model Training
Incorporate emerging deepfake variants through secure feedback loops and industry intelligence sharing.
Phase 8: Periodic Third-Party Audit
Schedule independent validation of detection effectiveness and maintain documented compliance evidence.
AI-Powered Strategies for False-Positive Avoidance
Advanced platforms reduce unnecessary escalations by applying layered contextual analysis. When a potential deepfake signal is detected, the system evaluates temporal consistency across multiple biometric modalities, alignment with declared executive profile, cross-reference with sanctions databases, and historical device patterns. This approach clears the vast majority of genuine executive verifications automatically while flagging genuine threats for human review.
Realistic Compliance Scenarios and Outcomes
A major trade-finance institution implemented multi-modal deepfake detection for executive approvals and reduced undetected synthetic media attempts by 87 percent while lowering manual review volumes by 69 percent. Another virtual asset service provider integrated real-time biometric scoring into its corporate onboarding workflow and successfully satisfied regulator inquiries with complete, explainable audit trails for every high-value verification.
These outcomes illustrate that deepfake risks to corporate KYC can be managed effectively through layered, audit-ready controls.
90-Day Implementation Checklist for Corporate KYC Hardening
Days 1–15: Assessment
- Map all executive video verification touchpoints
- Baseline current detection capabilities
- Assemble cross-functional team
Days 16–45: Technology Integration
- Deploy multi-modal liveness engine
- Integrate with sanctions screening
- Configure explainable AI models
Days 46–75: Testing & Tuning
- Run parallel verification in shadow mode
- Refine thresholds with live data
- Validate audit log completeness
Days 76–90: Deployment & Governance
- Transition to production monitoring
- Establish ongoing model retraining
- Schedule independent audit
Conclusion: Turning Deepfake Risk into Compliance Strength
Real-time deepfake executive impersonation represents a serious challenge to corporate KYC processes. Yet institutions that respond with layered, explainable detection controls and audit-ready frameworks can protect themselves while continuing to support legitimate high-value business activity. The organizations that act decisively today — upgrading verification technology, embedding contextual risk scoring, and maintaining comprehensive audit trails — will maintain regulatory goodwill and operational resilience in an increasingly sophisticated threat landscape.
Platforms purpose-built for regulated finance provide the infrastructure required to operationalize these defenses efficiently. Entities seeking to strengthen their corporate KYC controls are encouraged to evaluate integrated solutions that combine technical excellence with full regulatory alignment.
Request a Confidential Corporate KYC Deepfake Risk Assessment
