Blog
Chain Hopping via Cross-Chain Bridges

Understanding the Technique and Implementing Audit-Ready Detection Strategies for AML/CFT Compliance

Cross-Chain Bridges
In the evolving landscape of virtual asset service providers, trade finance platforms, and cross-border payment systems, one technique has emerged as a significant challenge for anti-money laundering and countering the financing of terrorism (AML/CFT) compliance teams: chain hopping. Also referred to as cross-chain bridging or multi-chain layering, this method involves moving value across disparate blockchain networks to obscure the origin and destination of funds. What once consisted of simple on-chain swaps within a single ledger has now evolved into sophisticated, bridge-mediated transfers that span multiple independent blockchains.
This comprehensive operational guide examines the mechanics of chain hopping, its implications for regulatory compliance, and — most importantly — the audit-ready frameworks and technology-enabled strategies that allow institutions to detect, monitor, and mitigate the associated risks while maintaining full adherence to FATF standards, Travel Rule obligations, OFAC and EU sanctions guidance, and local AML regulations. Every recommendation in this document prioritizes regulatory soundness, transparency, and explainable decision-making.
Chain hopping is not inherently illicit; many legitimate users employ cross-chain bridges for operational efficiency, cost optimization, or access to specialized decentralized finance protocols. However, when used as part of a layering scheme, it presents unique detection difficulties that traditional single-chain monitoring tools cannot address. Compliance professionals must therefore adopt multi-chain visibility solutions that preserve privacy where required while delivering regulator-grade audit trails.
Compliance-First Principle: Effective risk management of chain hopping requires programmable, cross-chain monitoring that embeds sanctions screening, Travel Rule data transmission, and false-positive reduction directly into the transaction lifecycle — without compromising operational speed or legitimate user experience.
Understanding Chain Hopping: From Simple Swaps to Bridge-Mediated Transfers
Historically, individuals seeking to obscure the source of funds relied on basic asset swaps within the same blockchain environment — converting bitcoin to ether or stablecoins on a single network. These intra-chain conversions could be tracked relatively effectively by on-chain analytics providers that maintained comprehensive address clustering and transaction graph databases.

Understanding Chain Hopping
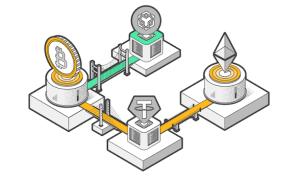
Chain hopping represents the next evolutionary step. The process typically follows this sequence:
- Value originates on a source blockchain (for example, as native tokens or wrapped assets on Solana).
- The assets are converted or wrapped into a bridge-compatible form.
- The wrapped assets are locked into a cross-chain bridge smart contract on the source chain.
- The bridge protocol releases equivalent value on the destination blockchain (for example, Avalanche), often in the form of a different native token or stablecoin.
- The process may repeat across additional chains, creating multiple hops before final off-ramping or further layering.
Cross-chain bridges act as the critical infrastructure enabling these transfers. They function as decentralized or semi-centralized custodians that lock assets on one chain and mint equivalent representations on another. Popular bridges include those connecting major ecosystems such as Ethereum, Solana, Avalanche, Binance Smart Chain, and layer-2 networks. Each hop introduces a new ledger, new transaction IDs, and new address clusters, effectively breaking the continuity that single-chain analytics rely upon.
The analogy frequently used in compliance training materials is that of a border crossing without customs records: funds appear to vanish from one jurisdiction (blockchain) and reappear in another with no visible linkage, unless the monitoring system maintains unified, cross-chain visibility. This fragmentation is precisely why chain hopping has become a noted technique in layering stages of money laundering typologies.
Why Chain Hopping Presents Unique Detection Challenges
Most legacy AML/CFT tools were designed for single-ledger environments. They excel at pattern recognition within one blockchain but lack native capability to correlate events across independent chains. When a transfer occurs via a bridge, the following breaks occur:
- Transaction hashes and addresses become non-overlapping between source and destination chains.
- Wrapped or bridged tokens often carry different contract addresses and metadata.
- Bridge smart contracts aggregate and redistribute value from multiple users, mixing legitimate and potentially illicit flows.
- Timing delays between lock and mint events further obscure direct cause-and-effect relationships.
As a result, even advanced on-chain analytics platforms that do not maintain dedicated cross-chain correlation engines frequently lose the trail. The funds effectively “disappear” at the bridge and “reappear” on the new chain under a new identity. This is the core reason compliance teams experience elevated manual review volumes and false-positive rates when dealing with bridged transactions.
Why Chain Hopping Presents Unique Detection Challenges
Regulators have recognized this gap. FATF guidance on virtual assets and virtual asset service providers explicitly highlights multi-chain activities as an area requiring enhanced due diligence. The Travel Rule, when applied to cross-chain transfers, demands that originating and beneficiary information travel with the value — yet many bridges operate with limited or delayed data-sharing capabilities, creating compliance friction for regulated entities.
Regulatory Expectations and Red Flags Associated with Chain Hopping
Financial institutions and virtual asset service providers are expected to implement risk-based approaches to cross-chain activity. Key regulatory expectations include:
- Continuous monitoring of bridge interactions involving customer addresses.
- Enhanced due diligence on counterparties that frequently use high-risk bridges.
- Maintenance of unified transaction graphs that span multiple chains.
- Integration of Travel Rule data transmission for any bridged value above applicable thresholds.
- Documentation of risk scoring methodologies for bridge-mediated transfers.
Common red-flag indicators that may trigger additional scrutiny include:
- Rapid sequential transfers across three or more distinct blockchains within a short window.
- Use of bridges known for limited KYC/AML controls or history of exploited vulnerabilities.
- Patterns of small “test” transfers followed by larger movements.
- Conversion through privacy-enhancing wrapped assets or mixers immediately before or after bridging.
- Addresses that interact exclusively with bridges rather than established decentralized exchanges or legitimate protocols.
When these indicators appear in high-volume trade or payment flows, compliance teams must apply layered controls to distinguish legitimate operational use from potential illicit activity.
Comparative Risk Matrix: Single-Chain vs. Cross-Chain Activity
| Aspect | Single-Chain Swaps | Chain Hopping via Bridges | Compliance Implication |
|---|---|---|---|
| Traceability | High (unified ledger) | Low (fragmented ledgers) | Requires dedicated cross-chain correlation |
| False-Positive Rate in Screening | Moderate | High (broken address links) | Elevated manual review burden |
| Travel Rule Applicability | Straightforward | Complex (multi-party bridge) | Demands enhanced data-sharing protocols |
| Sanctions Screening Effectiveness | Standard tools sufficient | Standard tools often insufficient | AI/graph-based multi-chain needed |
| Audit Trail Completeness | Readily available | Requires unified logging | Regulatory reporting more challenging |
Step-by-Step Playbook: Implementing Audit-Ready Cross-Chain Monitoring

Cross-Chain Monitoring
Phase 1: Risk Assessment and Bridge Inventory
Map all bridges used by customers or counterparties. Categorize them by risk level based on governance model, historical incidents, and KYC/AML controls.
Phase 2: Unified Cross-Chain Data Ingestion
Deploy systems capable of ingesting events from multiple blockchains simultaneously. Maintain a normalized transaction graph that links bridged events through cryptographic proofs or oracle attestations.
Phase 3: Programmable Compliance Rules at Bridge Points
Integrate real-time sanctions screening and Travel Rule data collection before value is released on the destination chain where technically feasible.
Phase 4: AI-Driven Pattern Recognition
Utilize graph neural networks and behavioral analytics to identify hopping sequences that deviate from legitimate user profiles.
Phase 5: False-Positive Reduction Layer
Apply contextual scoring that considers user history, business purpose, and volume patterns to clear legitimate bridge usage automatically.
Phase 6: Audit-Ready Logging and Reporting
Generate immutable, regulator-exportable records that document every cross-chain decision with full reasoning chains.
Phase 7: Continuous Model Training
Feed human analyst feedback into the system to improve detection accuracy over time.
Phase 8: Periodic Third-Party Validation
Engage independent auditors to certify the effectiveness of cross-chain monitoring controls.
AI-Powered Strategies for False-Positive Avoidance in Cross-Chain Environments
Modern compliance platforms reduce false positives dramatically by combining multi-chain graph analytics with natural language processing of on-chain metadata and behavioral profiling. When a potential hop is detected, the system evaluates:
- Historical interaction patterns of both source and destination addresses.
- Bridge-specific risk scores derived from industry-wide intelligence.
- Alignment with declared business activity (for example, legitimate DeFi yield farming versus unexplained rapid hops).
- Presence of required Travel Rule information.
This layered approach allows institutions to maintain high true-positive detection rates while clearing the majority of legitimate bridge usage automatically, thereby preserving operational efficiency.
Realistic Compliance Scenarios and Outcomes
Financial institutions and trade platforms that have implemented unified cross-chain monitoring report significant improvements. One large virtual asset service provider reduced manual bridge-related reviews by 78% while increasing detection of high-risk hopping patterns. Another trade finance entity integrated bridge monitoring into its sanctions screening workflow and successfully satisfied regulator inquiries with complete, explainable audit trails spanning multiple chains.
These outcomes demonstrate that chain hopping risks can be managed effectively when compliance infrastructure evolves alongside the technology.
Why a Purpose-Built Compliance Platform Is Essential for Cross-Chain Risk Management
Platforms designed specifically for high-volume trade and regulated finance environments provide native support for multi-chain monitoring, smart escrow mechanisms, and explainable AI decision engines. Such systems embed compliance logic directly into transaction flows, ensuring that bridge interactions are screened, documented, and reported in a manner that satisfies the most stringent regulatory expectations.
Key capabilities include real-time cross-chain correlation, automated Travel Rule data handling, and privacy-preserving techniques that share only necessary information with counterparties and authorities. These tools transform chain hopping from an opaque risk into a monitorable, manageable element of the overall compliance program.
90-Day Implementation Checklist for Audit-Ready Cross-Chain Monitoring
Days 1–15: Foundation
- Conduct comprehensive bridge usage audit across all customer flows
- Map current single-chain tools and identify coverage gaps
- Assemble cross-functional team including compliance, technology, and legal
Days 16–45: Technology Integration
- Deploy unified multi-chain data ingestion and graph engine
- Configure AI behavioral models for hopping pattern detection
- Integrate Travel Rule and sanctions screening at bridge interaction points
Days 46–75: Testing and Tuning
- Run parallel monitoring on live traffic in shadow mode
- Refine false-positive thresholds using historical data
- Validate audit log completeness with sample regulator scenarios
Days 76–90: Full Deployment and Governance
- Transition to production monitoring with automated alerts
- Establish weekly compliance review cadence for bridge activity
- Schedule first independent audit of cross-chain controls
A downloadable PDF version of this checklist, together with template policies and integration guides, is available through the secure platform portal.
Conclusion: Turning Cross-Chain Complexity into Compliance Strength
Chain hopping via cross-chain bridges represents a sophisticated evolution in virtual asset movement that demands equally sophisticated compliance responses. Institutions that treat multi-chain activity as a core risk vector — and invest in unified, AI-enhanced monitoring — position themselves to meet regulatory expectations while supporting legitimate innovation and operational efficiency.
The most effective programs combine technical visibility, programmable controls, and continuous human oversight. They reduce false-positive burdens, accelerate legitimate transactions, and generate the clear, explainable records that regulators require.
For organizations processing high-volume trade, payments, or virtual assets, a dedicated compliance platform that natively supports cross-chain correlation and audit-ready workflows provides the operational backbone needed to manage these risks confidently. Such systems enable teams to focus on genuine threats rather than overwhelming alert volumes.
Entities seeking to strengthen their cross-chain monitoring capabilities are encouraged to evaluate integrated solutions that align with the frameworks outlined in this guide. Proactive implementation today ensures regulatory resilience and competitive advantage in an increasingly interconnected blockchain ecosystem.